We all care about securing our data, but sometimes security feels infinitely more complicated than it’s worth. Between passwords, verification apps, face recognition, and multi-factor authentication, it’s hard to know what the best solution is for you and your company.
Think about what’s stored on your computer. If someone were to steal your password and hack into your account, what would they have access to? What information would be compromised?
In order to achieve greater data security, many companies are turning to and even starting to enforce Multi-Factor Authentication (MFA). With MFA, you reduce the likelihood that someone can hack into your account.
The Problem with Passwords
So why use multi-factor authentication when you can just use a password instead?
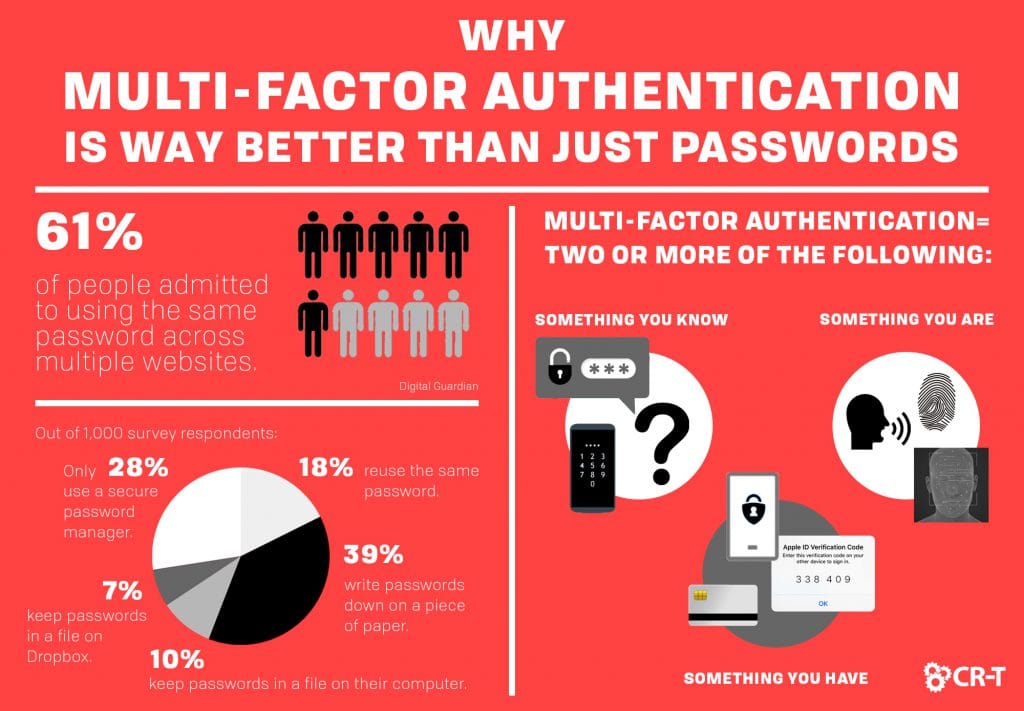
In 2018, Digital Guardian surveyed 1,000 people about their passwords and security habits. Their findings brought to light some startling statistics.
Passwords are Often Reused
According to the survey, 89% of consumers surveyed felt secure with their current password habits (Digital Guardian).
However, 61% of people admitted to using the same password across multiple websites (Digital Guardian). Interestingly enough, the group that was most likely to reuse passwords were individuals aged 18-24.
Passwords are Hard to Remember
- 18% reuse the same password
- 39% write them down on a piece of paper
- 10% keep them in a file on the computer
- 7% keep them in a file on Dropbox or another storage app
- 28% use a secure password manager
Multi-Factor Authentication: A New Approach
Clearly, passwords by themselves aren’t cutting it. Making a password easy to remember usually means that it’s easy to guess as well. And even if you create unique, secure passwords for each of your accounts, there’s still the challenge of figuring out how to store them all.
Unlike passwords, multi-factor authentication, or two-factor authentication, requires you to present two forms of credentials when logging into an account. That way, even if your initial password is compromised, your account will remain secure.
Types of Credentials
Your credentials can generally be broken into three categories:
- Something you know
- Something you have
- Something you are
The first type of credential is something we are all familiar with: what you know. This includes passwords, PINs, security questions, and other information you can recall. When setting up an account, you provide the system with this information, and the system remembers it so you can use this information to access your account in the future.
The second type of credential refers to an app, device, or object that allows you access to your account. This form of verification includes things like a smart card, an authenticator app, or a code sent to your phone, which you then enter into the website.
Finally, something you “are” refers to your biometrics—what makes you genetically unique from everyone else. Every time you use a fingerprint to open your phone or a face scan to log into your computer, you are utilizing this form of verification.
When is it Multi-Factor Authentication?
In order for verification be considered “multi-factor authentication,” you must enter two or more different forms of credentials. For example, if you swipe your debit card and then enter your PIN, you are engaging in multi-factor authentication.
More recent forms of MFA take the verification even further by tracking your behavior. Often referred to as adaptive authentication, this form of verification flags any login behavior that’s out of the ordinary.
For example, if you try to access your email from a new device, you might be required to enter new credentials, in order to verify that the person logging in is really you. This is the same reason that banks often freeze your credit card when they notice transactions taking place in a new location.
Why Multi-Factor Authentication?
MFA sounds great and all. But when is it actually necessary to implement multi-factor authentication, and when is a password sufficient?
You should use MFA whenever possible, but especially when it comes to your most sensitive data. This includes accessing your computer, your primary email, your financial accounts, and your health records.
Enhanced Security
The most obvious reason for MFA is that it provides an added layer of security. In order to access your account, a cyber criminal would need to steal both your password and your phone, for example. This decreases the likelihood that someone will be able to login as if they were you.
Greater Compliance
In addition to greater security, many businesses will implement MFA in order to remain compliant. At the federal and state level, many organizations are now required to use multi-factor authentication.
Even if MFA is not explicitly required, having greater security will bring you closer to compliance. And few passwords will protect your data quite as effectively as multi-factor authentication.
Ease of Use
Additionally, using multi-factor authentication is a lot easier than creating hundreds of passwords.
With most websites, you can choose to remember your device. This will allow you to frequently access a website from your home computer or phone, without having to use multi-factor authentication every time you login.
In addition, the added security of multi-factor authentication allows many companies to permit the use of single sign-on. This means that once you are authenticated, you are immediately logged in to your single sign-on software. You can then access a variety of apps, without having to sign into each one individually.
Peace of Mind
When your information is secure, you don’t have to spend as much time worrying about it and trying to protect it. This goes for both individuals and businesses.
According to Telesign, 86% of people say that multi-factor authentication makes them feel like their online information is more secure.
Finding the Right MFA Solution
Once you decide to make the switch to MFA, you still have to decide which solution is right for you. Luckily, there are a variety of options to choose from. When you understand your requirements and your business’s needs, you can better find a solution that will serve your employees and clients.
Understand Your Requirements
The first step to choosing an MFA solution is making sure you understand the needs of your organization. Do you plan to use multi-factor authentication for cloud apps, local devices, etc.?
Additionally, consider who will be using the MFA. Is it intuitive enough for your customers and employees? How easy is it to use? When you start considering the impact an MFA will have on your workflow, it will help you narrow down the options to those which will be most effective for your situation.
In order to maintain flexibility, don’t choose more than 2-3 verification factors. For most situations, anything more than this will negatively impact usability.
Choose Highly Available MFA Solutions
High availability refers to the performance and reliability of your MFA. This is especially important when it comes to security.
If your MFA solution goes down, your data will suddenly become accessible to anyone. That’s why you need to make sure you choose a highly available MFA solution.
We are share expertise in this category and are partnered to set you up with the best MFA and access management software found in the industry.
Consult a Professional
It can be overwhelming to try and make sense of everything an MFA has to offer. When you decide to implement multi-factor authentication, consult an expert in the field to walk you through the process.
At CR-T, we support a variety of verification methods. We even use multi-factor authentication among our own employees. If you have questions about which verification method is right for you, reach out to our team to schedule an appointment.
Stay Protected with Multi-Factor Authentication
It’s impossible to prevent every cyber attack, but having multi-factor authentication will make it more difficult for someone else to access your account.
Here at CR-T, we take pride in providing enterprise-level IT services at prices that work for small businesses. Our team of experts can become your IT support department, responding to issues quickly, often before you even know about them. Covering everything from your servers and network infrastructure, to your computers, workstations and mobile devices, we provide end-to-end solutions for all your technology needs.
Time and experience have helped us develop best practices and workflow procedures designed to keep your focus on your business, not your technology.