What does a hacker look like? Many people imagine a group of computer geniuses living in a foreign country. Or maybe you picture the classic guy wearing a black hoodie and sunglasses in a dark basement. But how often do you get to see the other side of famous hacks?
In this article, we’ll take you behind-the-scenes with two famous young hackers. By understanding their strategies, you can better prepare your business to withstand similar cyber attacks.
Hacker Kane Gamble, 15 Years Old
The year was 2016. 15-year-old Kane Gamble sat in front of a computer in his bedroom in Leicestershire, England. Through a series of social engineering techniques, he was able to gain access to some of the most secure accounts in the world.
According to an interview with a journalist, Gamble admitted that “it all started by me getting more and more annoyed about how corrupt and cold blooded the US Government are so I decided to do something about it.”
Gamble’s first target was John Brennan, the then director of the CIA. Gamble contacted Verizon, posing as a client of the company. He then used the information he had gained to pretend he was Mr. Brennan himself.
Initially, Gamble was denied access to the account because he could not name Mr. Brennan’s first pet. However, he was able to call the handler directly to change the account’s PIN and security questions.
Gamble used similar methods to access Mr. Brennan’s AOL account, along with his emails, contacts, iCloud storage account, and his wife’s iPad remotely. The data he accessed included sensitive information about military and intelligence operations in Afghanistan and Iran. He posted some of this information on Twitter and Wikileaks, taunting officials and harassing them about his access to the sensitive data.
Wreaking Havoc
But Gamble didn’t stop there. Shortly after hacking Mr. Brennan’s accounts, Gamble targeted Secretary of Homeland Security Jeh Johnson. Gamble took control of the secretary’s phone line, allowing him to access his voicemails and send texts through his phone. Gamble also harassed Johnson and his wife, sending them countless phone calls and threatening voice messages.
In October 2015, Gamble turned 16. A few months had passed, but his online criminal empire was growing. Gamble posed as the FBI boss to gain access to Mark Guiliano’s home accounts. He then used the information he found to enter the FBI’s Law Enforcement Enterprise Portal (LEAP).
Via the portal, Gamble had access to criminal intelligence records, in addition to the personal information of police officers and government employees. Gamble bragged: “This has to be the biggest hack, I have access to all the details the Feds use for background checks.”
The FBI noticed the breach and changed their password, but Gamble was able to call the helpdesk, pretending to be Mr. Guiliano, and have it changed again.
The final target was John Holdren, the senior science and technology adviser to Barack Obama. Gamble hacked all of Mr. Holdren’s personal accounts and sent them to an accomplice, who made hoax calls to the police and sent a SWAT team to Holdren’s home.
Game Over
Gamble’s reign of terror ended in February 2016, when he gained access to the US Department of Justice’s network. The records he accessed included the details of over 20,000 FBI employees and case files dating back several years.
Once the FBI realized Gamble had acquired this information, they contacted police in the UK, and Gamble was promptly arrested.
Gamble would not answer for his crimes until two years later, when he was tried in April 2018. He pleaded guilty to ten offences under the computer misuse act.
Hacker Eric Taylor, 12 Years Old
Eric Taylor was just like any other 12-year-old boy who enjoyed playing video games. Then one day, his game turned off unexpectedly through the actions of another player. Taylor learned that by installing certain types of software on his xbox, he could control the accounts of other players and kick them out of a game before they were able to beat him.
In a later interview with CNBC, Taylor shared, “Just imagine being 12 and having the power just to take anybody off your video game. So I felt a lot of power. And then I started learning other things and I moved on to joining a hacking group.”
It wasn’t long before Taylor had moved beyond hacking video games. Soon, he was learning to crash entire websites. In 2012, he and his hacking group were able to take Twitter offline for about an hour. He also claimed to have accessed data for hundreds of customer accounts, including those at corporations such as Amazon, Apple, AT&T, and Netflix.
He later told CNBC, “I wanted to get a message out there that nobody is safe online.”
Becoming Cosmo the God
Within a few years, Eric Taylor had become something of a celebrity among online hackers. He adopted the nickname Cosmo the God and began targeting celebrities and politicians. After accessing a person’s information, Taylor would post it online for the world to see. He shared social security numbers, home addresses, and even credit reports.
Perhaps Taylor’s most dangerous target was a group of Russian hackers who sold sensitive information. Taylor was able to hack into their website and then blackmail them for information, which they gave over immediately.
Taylor’s hacking career ended when the police located a malicious website with leaked information. Taylor had coded the website to make it look like it came from Russia, but the government tracked the postings back to him. He was arrested and sentenced to several years of probation.
Turning a New Leaf
But this story, at least, has a happy ending. Instead of harassing celebrities, Taylor now works as an advisor at the cybersecurity startup, Path. Path’s focus is to help companies make sure their websites are loading properly around the world.
Taylor feels that his life has completely changed despite his years of criminal behavior. “There is no way I could go back [to hacking’s dark side] after all the things that I went through to just be free and be here right now,” he said.
What We Can Learn From Hackers
Although these two hackers were different people, there are many similarities in the strategies they used to obtain sensitive information. For example, Kane Gamble hacked almost all of his targets through social engineering. He kept contacting different companies and accessing various accounts until he had the information he needed to create leverage over his victims.
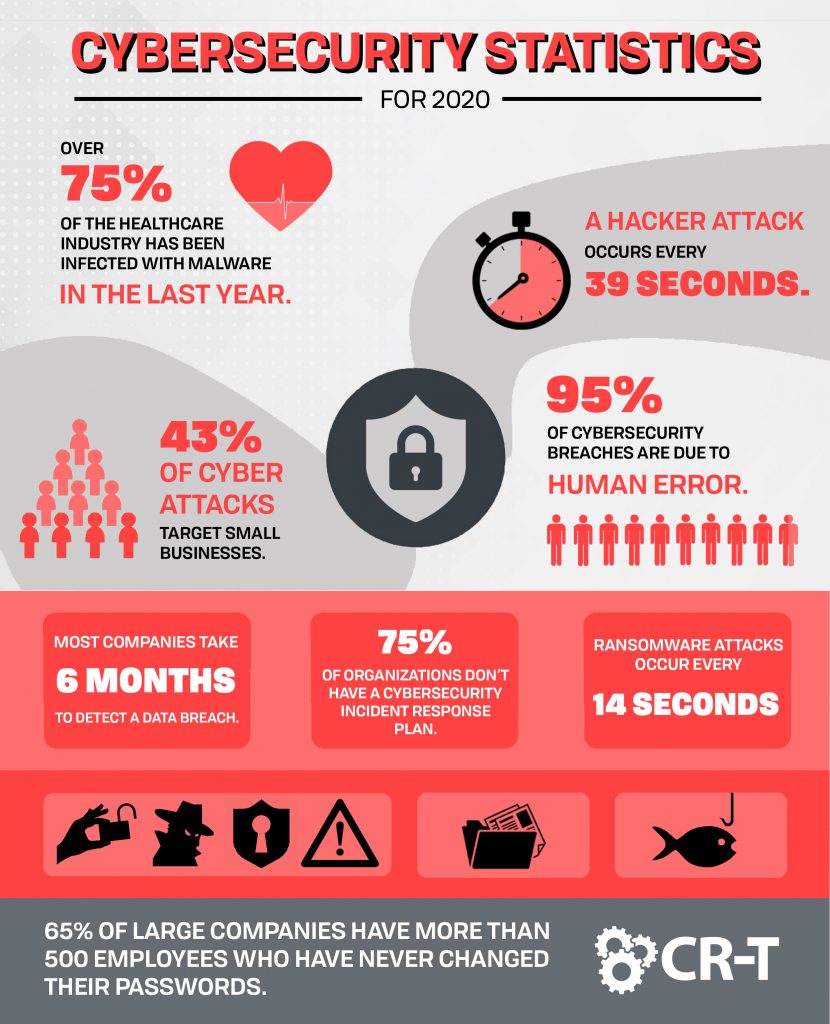
In order to protect yourself from cyber criminals, it’s important to implement strong security practices, like complex passwords, multi-factor authentication, and 24/7 monitoring to alert you of a potential breach. It’s impossible to prevent every cyber attack, but understanding the enemy will take you a step closer to protecting your business from common cybersecurity flaws.
Here at CR-T, we take pride in providing enterprise-level IT services at prices that work for small businesses. Our team of experts can become your IT support department, responding to issues quickly, often before you even know about them. Covering everything from your servers and network infrastructure to your computers, workstations and mobile devices, we provide end-to-end solutions for all your technology needs.
Time and experience have helped us develop best practices and workflow procedures designed to keep your focus on your business, not your technology.
Blog & Media
Cloud Services
Managed IT Support
Cyber Security
Project Services
Servers/Infrastructure
Firewalls
Networking
Hardware/Software
Microsoft Products/Cloud
Amazon Web Services
Penetration Testing vs Vulnerability Scanning
If you’re responsible for managing the security of your organization’s network or systems, you may have heard the terms “penetration testing” and “vulnerability testing” thrown
Backup and Disaster Recovery
Your organization can’t afford to neglect backup and disaster recovery. If it takes your business too long to get back online after a disaster, you
6 Steps to Secure Customer Data
Securing customer data is essential for one major reason: your business depends on it. As an IT director, you recognize the importance of cybersecurity when
5 Steps to Promote Compliance in the Workplace
You’re familiar with the ever-changing world of regulatory compliance. Robust compliance enables you to avoid legal liabilities while improving your organization’s effectiveness. And many of