Email phishing allows cyber criminals to target specific users. Criminals deliver fraudulent email messages, with the intent to steal critical information or infect the user’s device with dangerous malware. Phishing attacks are becoming more sophisticated, making it more important than ever for businesses to have a response plan in place for detecting, preventing, and responding to email phishing. By implementing the necessary security measures and learning how to identify phishing emails, you can protect your business from this ever-growing security threat.
Email is a unique form of attack, because it uses social engineering to deceive a user into downloading or permitting malicious content.
And phishing is only becoming more effective. According to Retruster, 90% of data breaches are caused by phishing.
Additionally, phishers are now moving past attacking individuals to attack entire organizations. This means that it’s more important than ever to know how to handle phishing emails.
What is Email Phishing and Why is it Dangerous?
Email phishing is an online scam that appears to be legitimate. Phishers are cybercriminals that try to retrieve personal information, often by instructing you to follow a link or asking you for the information directly. Some scammers already have access to a portion of your information, and they may use this to try and gain your trust.
Furthermore, phishing messages often appear genuine, making them even harder to detect as they become more advanced.
Phishing may present itself in many forms. Some emails are sent out to hundreds of users, in the hopes that at least a few of them will be fooled and fall susceptible to the scam.
Types of Phishing
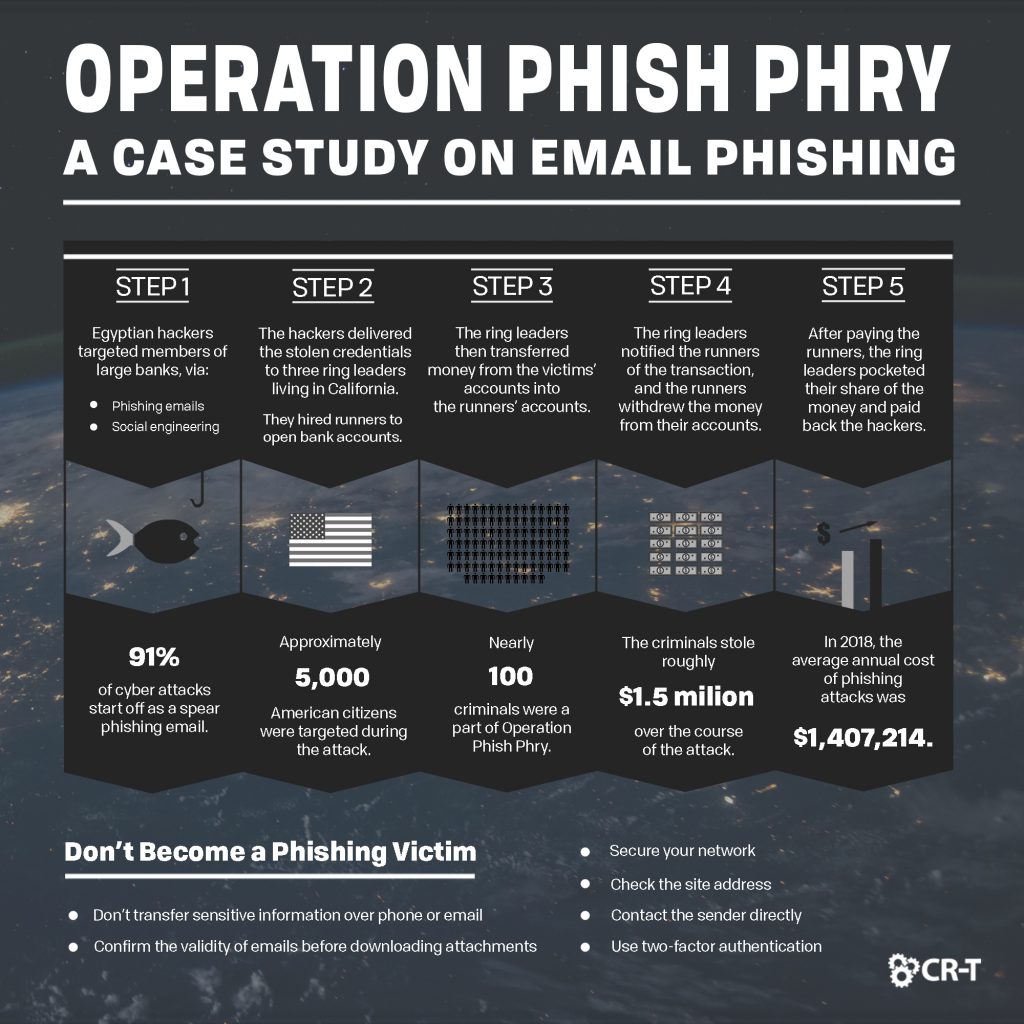
But most phishing emails are becoming increasingly more targeted. “Spear Phishing” targets a specific individual or organization in order to seek unauthorized access to sensitive information. “Clone Phishing” occurs when someone is able to steal and clone an email address in order to make email messages look legitimate. The criminals then send the infected email to an unsuspecting user.
Another form of phishing, called whaling, occurs when phishers target high-profile employees in an effort to obtain sensitive information. Sometimes, scammers will impersonate managers and company leaders. Unsuspecting employees are then tricked into giving out confidential information or transferring money into fraudulent accounts.
What could a phishing attack cost you?
Severe cases of phishing can cost companies millions of dollars. The Ponemon Institute revealed that some of the most successful phishing attacks in 2016 earned attackers up to $3.7 million.
With access to account credentials and/or sensitive information, cyber criminals can hijack usernames and passwords, leaving accounts compromised. This also gives them the ability to change account passwords, steal money or credentials, or sell information to third parties.
Due to its high frequency and deceptive nature, email phishing poses a variety of risks. On the surface, email phishing can lead to a large degree of equipment damage, stolen funds, and identity theft. These attacks might also induce greater financial loss for companies, due to investigation costs, increased insurance premiums, regulatory fines, and damage to the company’s reputation.
How Can I Detect Email Phishing?
Phishing emails are particularly dangerous because they may not initially look fraudulent. However, there are several clues you can look for that might indicate a scam. If you receive an email from a company with which you don’t have an existing account, or if an email asks for personal information, like passwords and credit card numbers, you are very likely dealing with a scam.
Yet many fraudulent emails appear legitimate. They might even look like they’re from a company that you know and trust, like a bank. So how can you detect spam among emails that aren’t as obvious?
Watch for Red Flags
There are several details you can pay attention to that might indicate email phishing.
If you receive an email from a company with which you have an account, they will usually call you by your first name, so an email without a personal greeting might raise a red flag. Some phishing emails also contain poor grammar and misspellings.
However, almost every fraudulent email will try to get you to click on a link or open an attachment. They use scare tactics or urgent requests in order to motivate the user to take immediate action. If you receive an email that urges you to follow a link, be aware that it might be a scam, even if everything else about the email seems normal.
Train Your Employees
One of the best ways you can protect yourself from email phishing is to train your employees to recognize fraudulent emails. In 2015, Mcaffee discovered that 97% of consumers are unable to recognize a phishing email. Employees can become your greatest risk if they aren’t prepared to respond to an attack.
Hold one or more training sessions in which you discuss the signs of phishing emails and create a plan for responding to them.
At CR-T, we offer frequent phishing training for our own employees, and we can provide this same service for you and your employees.
What Can I do to Prevent Email Phishing?
You can protect yourself against email phishing by learning how to recognize and respond to phishing emails when you receive them.
Don’t open emails from unknown senders and avoid clicking links embedded within the email. According to Proofpoint, 50% of phishing sites now use https, meaning that you can’t necessarily trust a link, even if it looks secure. Instead, enter the website address directly into your browser, or search for it on Google.
If you receive an email claiming to be from a company you know and trust, you can contact the company by phone or through their website. Instead of following a link through your email, access the website using your own link, or search for it online.
If there is truly an error with your account—or if some other action is required—you can solve the issue directly through the company, without having to click on any suspicious links.
Secure Your Network
In addition to following smart practices, secure your network through antivirus.
According to Alert Logic, 92.4% of malware is delivered via email. An antivirus solution will prevent viruses from entering your computer through your email and protect you if you accidentally download dangerous attachments.
Antivirus will also automatically block dangerous websites, helping you stay protected if you unintentionally follow a malicious link.
Be aware that antivirus won’t stop you from receiving fraudulent emails. Antivirus can prevent phishing emails from infecting your computer, but you still need to be smart when deciding whether to follow a link or open an attachment.
In addition to antivirus, spam filters can help you detect and transfer spam mail to a separate location.
Wombat Security estimates that 97% of businesses utilize email/spam filters to safeguard against phishing. Spam filters detect and block fraudulent emails before they can reach the user’s inbox, protecting you from spam, viruses, malware, email phishing, and other attacks.
By implementing these security measures, you can mitigate the amount of spam you receive and reduce the risk of an attack.
How do I Respond to a Phishing Attack?
Keep Yourself Protected
One of the best ways to protect yourself against security threats is to have an incident response (IR) procedure in place. Make sure all staff are trained on what to do if any accounts or devices are compromised.
If you fall victim to a phishing attack, change your computer password, your email password, and any other passwords you think may have been compromised. Update your software and run a virus scan to see if your device is in danger. If you have a spam filter, adjust the perimeter email filters to block similar messages to the one sent in the fraudulent email.
Save any information you can, in case you need to take further action.
- Obtain a copy of the email with full headers and original attachments, including a copy of the IP address.
- Use a threat intelligence site to check the IP address. Search the web for any information regarding the sender, subject line, message ID, source IPs, or file attachment names.
- Check the sender details to see if you can identify the fraudulent email address—or website name—and notify credit agencies of the fraudulent email.
- Report all phishing emails to the Federal Trade Commission (FTC) and the Anti-Phishing Working Group.
After taking the necessary steps to secure your network, continue to monitor the account for any unusual behavior. Check all accounts regularly for suspicious activity. Keep a list of known phishing sites to prevent a future attack.
Learn From Your Mistakes
Although no one wants to fall prey to a phishing email, you can use any negative experiences to better train your employees and help them take email phishing seriously. Teach them to be skeptical about following links sent through email. Use phishing tests and security awareness training to keep them prepared for future threats.
Security solutions, combined with smart behavior, will prepare you to respond to the dangers of email phishing. We want to help you stay protected. Our team of experts can provide you with the resources you need to maintain an efficient and secure network.
Start Today—Get a Free Consultation
Here at CR-T, we take pride in providing enterprise-level IT services at prices that work for small businesses. Our team of experts can become your IT support department, responding to issues quickly, often before you even know about them. Covering everything from your servers and network infrastructure, to your computers, workstations and mobile devices, we provide end-to-end solutions for all your technology needs.
Time and experience have helped us develop best practices and workflow procedures designed to keep your focus on your business, not your technology.
Blog & Media
Cloud Services
Managed IT Support
Cyber Security
Project Services
Servers/Infrastructure
Firewalls
Networking
Hardware/Software
Microsoft Products/Cloud
Amazon Web Services
Penetration Testing vs Vulnerability Scanning
If you’re responsible for managing the security of your organization’s network or systems, you may have heard the terms “penetration testing” and “vulnerability testing” thrown
Backup and Disaster Recovery
Your organization can’t afford to neglect backup and disaster recovery. If it takes your business too long to get back online after a disaster, you
6 Steps to Secure Customer Data
Securing customer data is essential for one major reason: your business depends on it. As an IT director, you recognize the importance of cybersecurity when
5 Steps to Promote Compliance in the Workplace
You’re familiar with the ever-changing world of regulatory compliance. Robust compliance enables you to avoid legal liabilities while improving your organization’s effectiveness. And many of