Many of last decade’s science fiction is now becoming a reality. You might have seen ads for a smart fridge or a self-driving car, but that seemingly “far-fetched” technology isn’t as far away as you might think. The Internet of Things is growing every year, with new forms of technology that work to make our lives easier. But these devices also come with a plethora of security risks. In order to safely enjoy the benefits that the IoT has to offer, it’s important to understand IoT security so you can protect your organization from outside threats.
What is the Internet of Things?
Billions of devices are connected to the Internet every day. And not all of these devices are computers and cell phones. The Internet of Things (IoT) moves beyond traditional Internet devices to include like smart watches, motion sensors, and self-driving cars.
For example, a doorbell camera is an IoT device that allows you to check and answer your front door from any location. It constantly monitors your doors and captures motion changes when someone walks by. Amazon Alexa is another IoT hub, acting as both a smart speaker and virtual assistant.
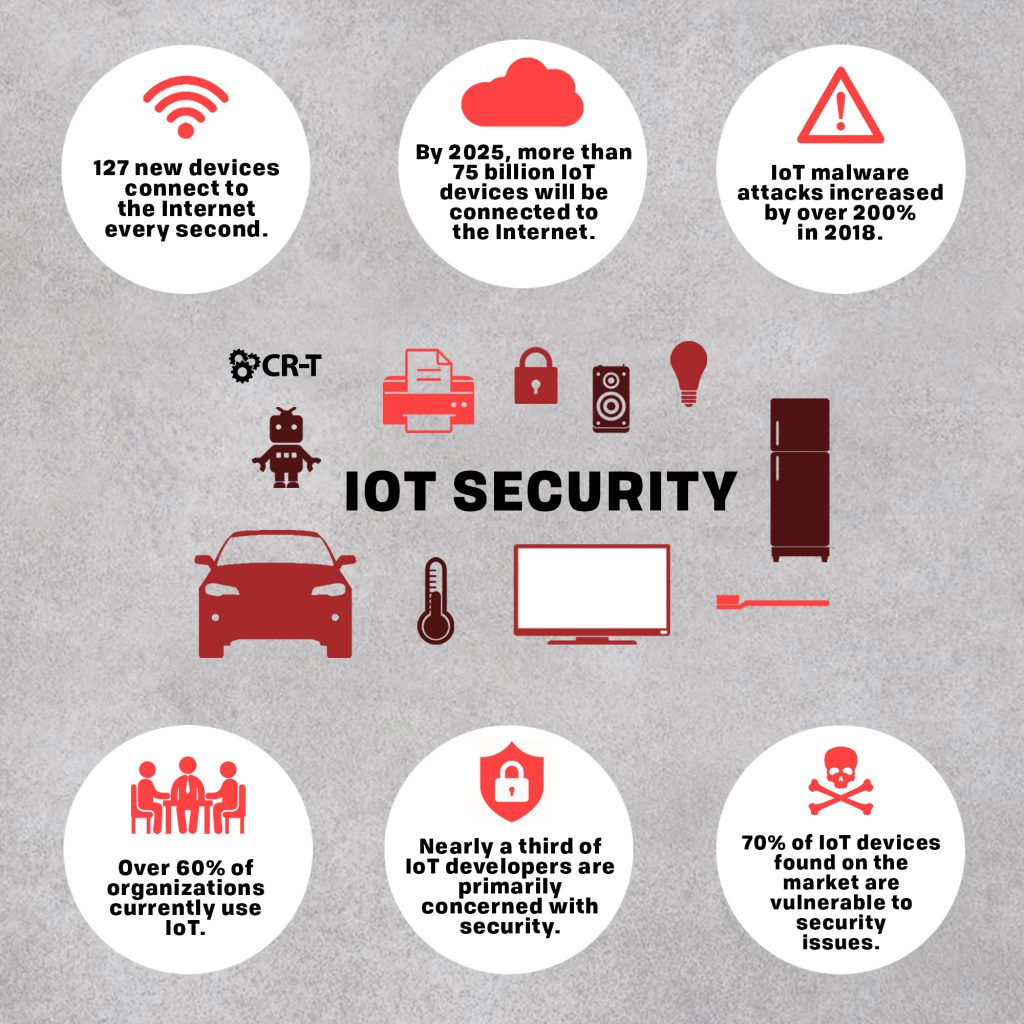
The IoT is a web of devices that continues to grow every year. IDC predicts that by 2025, there will be 41.6 billion devices connected to the IoT. And Gartner believes that the enterprise and automotive sectors will account for 5.8 billion devices this year.
IoT Benefits
Imagine driving to your house after a long day of work. Your car automatically connects to your smart devices back home, allowing you to listen to Spotify, Audible, and Pandora, all without having to connect to your phone. While driving, your car predicts points of congestion along the way, allowing you to follow the fastest and safest route back home.
As you pull into your driveway, an IoT sensor automatically opens your garage door. You turn off the car and approach your front door, which is protected by a smart lock and motion sensors. You walk through the front door and into your kitchen, whose lights have been scheduled to automatically turn on at the same time every day. You tell your thermostat to set the room to 72° as you settle on the couch and ask Alexa to start up your favorite TV program.
IoT Devices for Businesses
- Effortless communication
- Easier access to information
- Greater automation and control
- Time savings
- Energy savings
- Cost savings
IoT Security Risks
Although the Internet of Things allows for greater convenience and control, it also comes in a variety of risks.
According to Entrepreneur Media, 70 percent of IoT devices found on the market are vulnerable to security issues. These security risks open the door to hacking, privacy breaches, and theft.
In order to safely navigate the Internet of Things, it’s important to understand IoT security risks and how to avoid them.
What are the Risks?
Some IoT security risks stem from the devices themselves. In 2017, ZDNet shared research findings that revealed over 175,000 IoT cameras carried a flaw that allowed them to be easily hacked. Cyber criminals could access the devices remotely and then use them for surveillance, botnet attacks, and attacks against other devices on the network.
Among the top IoT security risks are hardware issues, a lack of a secure update mechanism, botnet attacks, hijacking, and rogue IT devices. However, a large number of security risks result from user error. A lack of knowledge and awareness of IoT devices can lead to problems like social engineering attacks.
Managing IoT security risks requires a combination of high-quality manufacturing and user awareness. Both the manufacturer and the user are responsible for preparing the device to withstand security threats and preparing the user to understand how to combat these threats.
Privacy Concerns
In addition to hijacking and other attacks, the Internet of Things involves a new layer of privacy concerns. Smart devices are designed to remember your preferences, but their wealth of knowledge also makes them vulnerable.
The data smart devices collect makes it very easy to paint a picture of you. If that data is stolen or sold to another party, you run the risk of others accessing your personal information. Sometimes, the information shared is simply your name or email address, but other times, it could be your account information, passwords, or credit card number.
When you purchase or connect an IoT device, it’s important to understand the privacy agreement so you can protect any information your device remembers. Otherwise, that information can be made available for anyone to see.
Protect Connected Devices
All forms of technology come with security risks, and the IoT is no different. So how can you protect your devices from hijacking and other threats?
Before purchasing an IoT device, make sure you understand whether the design is secure. Get as much information as you can from the provider, and don’t be afraid to walk away if the design doesn’t meet your standards.
Before you connect your device to the Internet, weigh the benefits with the security risks. Many smart device features are available without an Internet connection, which will protect your security and save you the additional Internet costs.
If possible, use a secondary network connection that’s separate from your primary wifi network. That way, you can put all of your smart devices on a separate network and more easily restrict who has access to them.
Finally, follow best practices when it comes to IoT security. Use strong passwords, and change them frequently. Use a VPN if you want to provide even greater security for your connected devices. Keep an eye out for ways that others might be able to access your devices, like through social sharing.
By paying attention to potential security risks, you can keep your smart devices protected and maintain a high level of IoT security.
The Future of IoT Security
As the Internet of Things grows, it’s becoming cost-effective to add more devices to the IoT. Certainly, smart devices make life more convenient, but they can also add a great deal of risk if you aren’t careful. Understanding IoT security will keep you and your organization safe as you take advantage of the benefits that IoT has to offer.
Here at CR-T, we take pride in providing enterprise-level IT services at prices that work for small businesses. Our team of experts can become your IT support department, responding to issues quickly, often before you even know about them. Covering everything from your servers and network infrastructure to your computers, workstations and mobile devices, we provide end-to-end solutions for all your technology needs.
Time and experience have helped us develop best practices and workflow procedures designed to keep your focus on your business, not your technology.
Blog & Media
Cloud Services
Managed IT Support
Cyber Security
Project Services
Servers/Infrastructure
Firewalls
Networking
Hardware/Software
Microsoft Products/Cloud
Amazon Web Services
Penetration Testing vs Vulnerability Scanning
If you’re responsible for managing the security of your organization’s network or systems, you may have heard the terms “penetration testing” and “vulnerability testing” thrown
Backup and Disaster Recovery
Your organization can’t afford to neglect backup and disaster recovery. If it takes your business too long to get back online after a disaster, you
6 Steps to Secure Customer Data
Securing customer data is essential for one major reason: your business depends on it. As an IT director, you recognize the importance of cybersecurity when
5 Steps to Promote Compliance in the Workplace
You’re familiar with the ever-changing world of regulatory compliance. Robust compliance enables you to avoid legal liabilities while improving your organization’s effectiveness. And many of