The world of technology is complicated and ever-changing. But there are a few constants when it comes to areas of security and the cloud. In this article, we compiled 7 hilarious tech quotes to illustrate some important facts when it comes to security.
How to Navigate the Internet of Things Safely
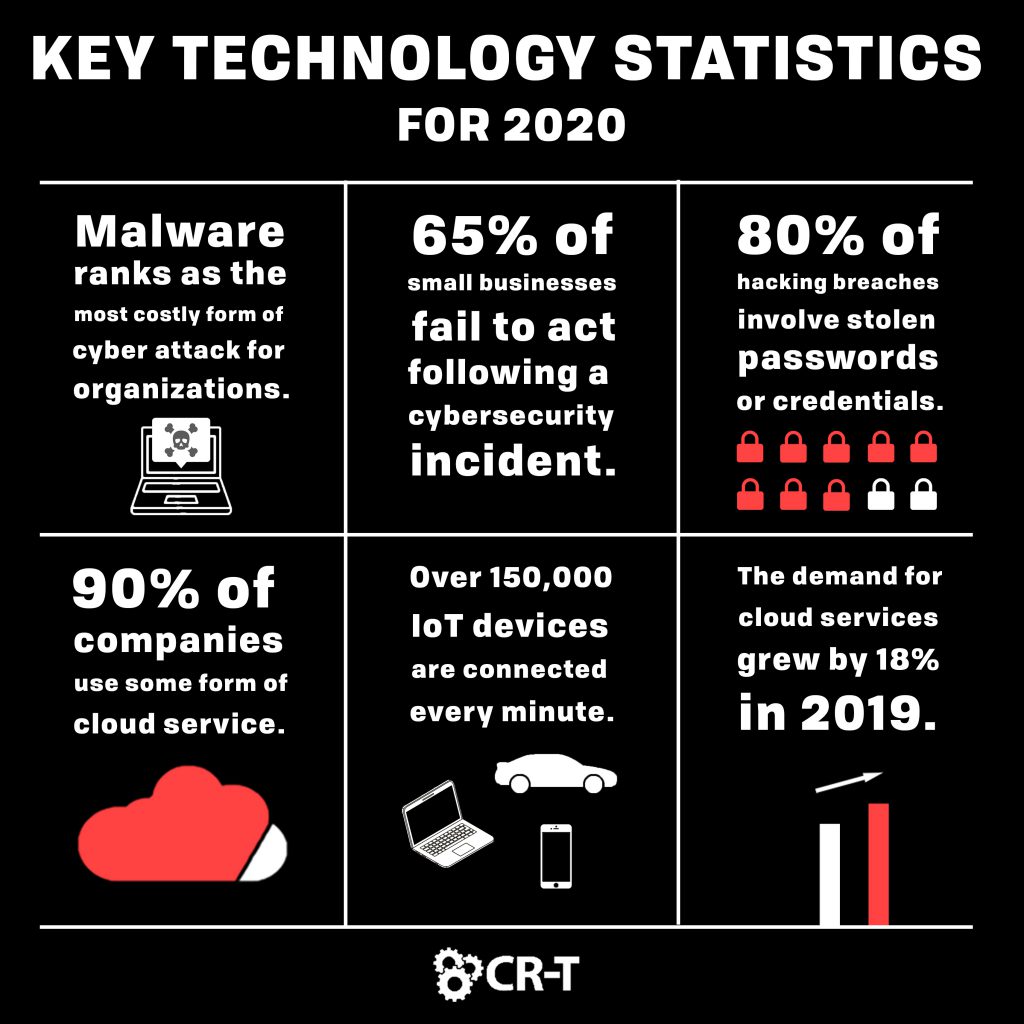
Billions of devices around the world are connected to the Internet. By 2021, there are expected to be 25 billion Internet of Things (IoT) devices. And there are currently over 150,000 IoT devices connected every minute (SSL Store).
Certainly, the IoT has advanced technology for individuals and businesses. Many IoT technologies have increased security, like home security systems and applications.
However, the IoT is also creating a lot of problems when it comes to security. Smart devices are constantly collecting data—in some cases very sensitive data. And many IoT devices lack the capability to be patched, which leaves them vulnerable and permanently at risk.
As your business continues to expand the number of devices you can access, it will be more important than ever for you to prioritize strong security. Unfortunately, due to the diverse number and type of IoT devices, there is no “one size fits all” solution when it comes to IoT security.
The good news is you can still take measures to understand the risks that are affecting your business. Start with a risk assessment that analyzes the vulnerabilities within your network. As you discover how the IoT is affecting your business, in particular, you will be more prepared to respond to existing threats.
Cybersecurity is About More Than Just Firewalls
Security is constantly evolving, especially as cybersecurity threats continue to grow. Malware still ranks as the most costly form of cyber attack for organizations, according to Security Boulevard. And a KnowBe4 report found that 96% of respondents view email phishing scams as their top security risk.
It’s easy for security to feel overwhelming, and you might not know how to prioritize your security needs. Managed security service providers can help you by providing a security audit of your business and its systems.
Following the audit, you will have a comprehensive view of your cybersecurity, which will make it easier to find the gaps in your security and create a plan for moving forward.
Is Your IT Department Wearing Blinders?
According to Top VPN Review, 65% of small businesses fail to act following a cybersecurity incident. For many of these businesses, they didn’t know there had been a breach in the first place.
It’s important to have a solid understanding of your business’s security so you can prevent attacks and other threats. However, no one can be 100% protected 100% of the time.
In addition to strong cybersecurity, make sure you have policies in place for responding to security breaches and potential threats. Implementing behavior analytics will help you detect unusual activity more quickly. This could greatly reduce the amount of downtime you experience during a breach.
If your organization experiences a data breach, start by contacting the necessary personnel, including a team of IT professionals, your data breach response team, any support vendors, and a forensic team, if necessary.
Locate the threat and work with IT professionals to keep the damage from spreading. Collect as much information as possible, and notify any affected parties. By understanding how the breach started, you can prevent future threats from affecting your security.
What a Cyber Attack Could Mean for Your Business
- Multi-factor authentication
- Privilege access management
- Behavior analytics
- Employee security awareness training
- Strong compliance

Why Everybody is Talking About the Cloud
90% of companies use some form of cloud service (451 Research). And the demand for cloud services grew by 18% in 2019 (Sys Group).
While you might be hesitant to migrate to the cloud, there are several benefits in making the switch. The cloud offers a great degree of flexibility, as it allows you to scale your workload according to your needs. Additionally, cloud backups and disaster recovery solutions provide greater security than you could obtain with an on-premise solution.
Maybe you aren’t sure if the cloud is the right fit for you. Or perhaps you don’t know which cloud option will best serve your business. An MSP can help you consider all of your options and answer your questions as they relate to managed cloud services.
Password Best Practices in the Security World
According to LastPass, 80% of hacking breaches involve stolen passwords or credentials. One of the best things you can do to prevent a cyber attack is impeding attackers from accessing the information in the first place. Strong passwords and credentials will protect your account from surface-level threats.
The difficulty with passwords is that by making them easy to remember, you also make them easier to guess. However, complicated passwords are often harder for the user to remember, which can negatively impact productivity.
There are a few tips you can implement to strengthen your password use. Avoid using personal information in your passwords. Instead, think of a phrase that will be easy for you to remember, and substitute some of the letters with numbers and symbols.
A password manager can also help you keep track of dozens of passwords, without having to remember them all. You can download software, apps, or even create a password-protected document to help you easily store and manage your passwords.
Many organizations are implementing multi-factor authentication—in addition to passwords—due to the massive impact it has on security. Instead of a single password standing between a hacker and your data, you can create multiple layers of security. And many forms of authentication are very simple for users to implement. This means you can maintain efficiency while increasing your security.
If it Smells, Throw it Out.
At a minimum, outdated tech is dangerous because it makes you more susceptible to security breaches. But it also has the potential to affect your productivity, business growth, and reputation. A Microsoft survey found that 90% of people would stop doing business with a company due to outdated technology.
Make sure you frequently update your software and applications. Most programs allow you to opt-in to automatic updates so you don’t have to keep track of them all. If you can’t implement automatic updates, make sure you are updating your technology at least once a month.
Additionally, you should replace your hardware at least every 5 years. Create a schedule for testing and replacing technology to ensure you are never using outdated systems. Replacing hardware costs money, but it will save you a lot more in the long run by increasing efficiency and preventing data loss.
Make Smart Decisions Regarding Technology
Managing your company’s technology is a big job, but you will be successful as you prioritize security and educate yourself on the best ways to implement technology in the workplace.
Here at CR-T, we take pride in providing enterprise-level IT services at prices that work for small businesses. Our team of experts can become your IT support department, responding to issues quickly, often before you even know about them. Covering everything from your servers and network infrastructure to your computers, workstations and mobile devices, we provide end-to-end solutions for all your technology needs.
Time and experience have helped us develop best practices and workflow procedures designed to keep your focus on your business, not your technology.
Blog & Media
Cloud Services
Managed IT Support
Cyber Security
Project Services
Servers/Infrastructure
Firewalls
Networking
Hardware/Software
Microsoft Products/Cloud
Amazon Web Services
Penetration Testing vs Vulnerability Scanning
If you’re responsible for managing the security of your organization’s network or systems, you may have heard the terms “penetration testing” and “vulnerability testing” thrown
Backup and Disaster Recovery
Your organization can’t afford to neglect backup and disaster recovery. If it takes your business too long to get back online after a disaster, you
6 Steps to Secure Customer Data
Securing customer data is essential for one major reason: your business depends on it. As an IT director, you recognize the importance of cybersecurity when
5 Steps to Promote Compliance in the Workplace
You’re familiar with the ever-changing world of regulatory compliance. Robust compliance enables you to avoid legal liabilities while improving your organization’s effectiveness. And many of